Hello, friends,
Ever since my Twitter account was hacked a decade ago—because of a weak password—I’ve been passionate about creating and using better passwords. I use a password manager for most accounts, and my most important passwords are long word combinations that are stored both in my head and using pen and paper.
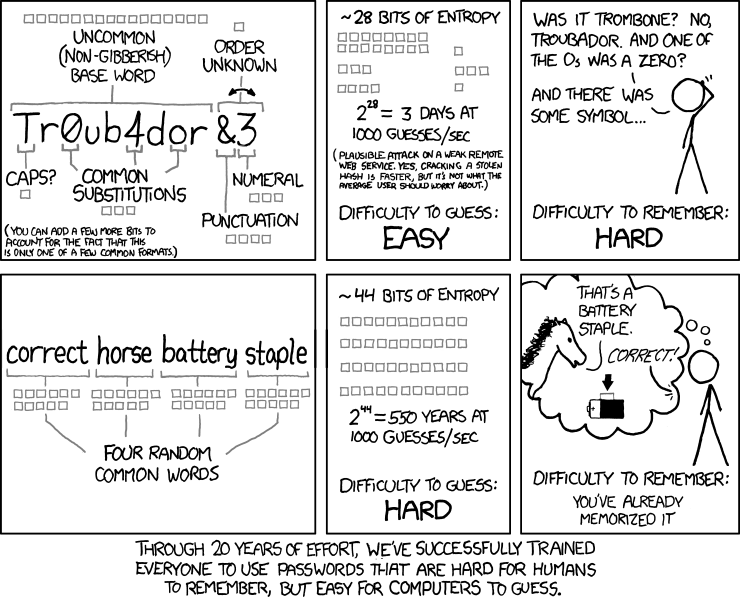
The method I use to make my important passwords is called Diceware. By rolling dice, I come up with random numbers and use those numbers to pick words from a word list where each word is assigned a number. The resulting password is a series of dictionary words that is easy for me to remember and hard for a computer to crack.
The computer science measure of how hard a password is to crack is something called “entropy.” The longer the password, the more entropy it has. I use six-word Diceware passphrases, which Diceware creator Arnold Reinhold says has 77.5 bits of entropy. That means, he writes, a six-word passphrase is only “breakable by an organization with a very large budget, such as a large country’s security agency.”
I am so invested in this method that when my daughter was 8 years old, I started paying her to roll dice and make Diceware passwords for me. She eventually turned it into an online business that she still operates to this day.
But this summer I heard some news about passwords that blew my mind. Jeremi Gosney, a renowned password cracker, gave a talk at a hacker conference and declared that entropy was overrated. The most important feature of a strong password these days, he said, was uniqueness—having a different password for each account.
Gosney is password royalty. He helped develop the open source password recovery software Hashcat, and he is the former CEO of the password-cracking firm Terahash. He helps run the DEF CON Password Village and the PasswordsCon track at Security BSides Las Vegas. So I called him up and asked him to explain the new thinking in the password world.
Our conversation, lightly edited for brevity and clarity, is below.
Angwin: To start, what is password cracking, and what does this profession look like?
Gosney: Typically, when we talk about password cracking, we’re talking about offline password cracking, which is where someone has obtained a copy of a password database. The passwords in the database are almost never in plain text (text humans can read with their eyes). They’re scrambled using what’s called a hash function. The only way to crack a password is essentially to play a guessing game, where you run password guesses through the same hash algorithm that was used to produce the hashes in the database, and you compare the results. If you end up with two hash values that are the same, then we know what the password was. There’s also online password cracking, which is where someone is either typing into a log-in field to manually guess passwords, or they’re using a computer program to automatically try values in that form field.
We focus on offline cracking, where someone has a copy of the password database, and it doesn’t mean they’ve obtained this illegally. Some people, like the information security team of a corporation, will intentionally try to crack the corporation’s passwords to test the effectiveness of their corporate password complexity policy. They want to identify the weak passwords before a malicious actor can. Another legitimate case for password cracking is if someone in accounting encrypted a spreadsheet and then got hit by a bus and other employees needed access to that document. The enterprise might attempt to crack the password for the document or hire someone like me to do that. There’s a plethora of legitimate use cases.
Angwin: Can you talk about the role of breaches in password cracking and how common they are?
Gosney: Prior to 2010, we were quite naive in the way that we guessed passwords. What happened in 2009 was that a large site, rockyou.com, with more than 32 million users, got hacked. This website stored all its users’ passwords in plain text, and all the passwords were leaked. That gave us the single biggest insight into how humans construct passwords globally. It was unprecedented. That lit a bonfire under the password-cracking world because suddenly we had some amazing new input values for cracking password databases. Every password leak that has happened since just widens our window into how people create passwords. We have dozens of major password leaks every year. Another major one was the LinkedIn breach revealed in 2016, which we were able to crack to about 96 percent over the course of a week.
Compiling RockYou, LinkedIn, Ashley Madison, and other big leaks, we have a really strong picture of people’s passwords. We analyze this data to make more targeted guesses in the future as to what people’s passwords are. It’s a feedback loop; we crack passwords, add them to our word list, and use those to crack new passwords.
Angwin: You have said that password cracking is more of an art than a science, specifically that it requires knowledge of human psychology. First, can you talk about the mathematical components of password cracking and then explain how psychology plays into it?
Gosney: The mathematics is really the hash algorithm we spoke about. When people hear that we crack passwords, they think that we’re writing a lot of code, but it’s more simple than that. We take the same hash function that was used to create the hashed passwords, and we try to guess what the input value was. That’s where the art comes into it; despite what software they are using, the password cracker is only as good as the guesses they make. The brain is the password cracker. The software and the hardware, these are the tools we use, but the hammer and chisel don’t define the carpenter. The carpenter is the artist doing the work.
That’s where the psychology portion comes in. Typically, the passwords that we can crack aren’t the ones that are generated by machines. (The only way to crack random passwords is through brute force, incrementally trying every character in order.) Where we find the most success as password crackers is targeting passwords that are generated by humans, because humans across the globe still tend to think alike. Despite our language and cultural differences, our brains are only capable of coming up with a finite space of patterns. We have honed our methodologies to exploit these patterns. Everyone still tends to think alike globally when we tell them to come up with a short secret. It’s that human element that we’re exploiting in the password-cracking process.
Angwin: What is it that we humans all do similarly?
Gosney: If I told you to think of a short string that is six characters or more, you’re probably going to pick something that you’re interested in, a hobby or interest, or a city or sports team, or your kids’ or pets’ names. People come up with something that is at the forefront of their mind or close to their heart.
With password complexity policies that require an uppercase character and a number, 99 percent of the people on this planet are going to put the uppercase character in the first position and the number in the last position. Of course some people deviate, but the vast majority are going to follow very simple patterns. Armed with a bit of knowledge, such as a common dictionary, famous landmarks, sports teams, first names, last names, and pets’ names, we can crack 99 percent of a password database in less than a week.
Angwin: I was taught that I should make my passwords long and complex in order to make them unbreakable. But you recently gave a talk saying that was the wrong approach. Explain.
Gosney: I think we need to take a major step back and look at all the different ways that passwords are actually compromised in the real world. As you go through the threat model, the cases where complexity and length matter are very few and far between. In fact, pretty much the only case where complexity and length matter is when we’re defending against offline password cracking. But for every other case in the threat model where passwords are stolen, length and complexity simply don’t matter.
Most passwords are stolen in plain text, not from these hashed databases that people like me try to crack. They are stolen through phishing attacks, or malware, or shoulder surfing. So length and complexity don’t matter. Using unique passwords for each account is what matters because it prevents the attacker who has stolen one of your passwords from accessing more than one of your accounts. It contains the scope of the breach to only the single compromised account.
Angwin: So, does that argue for having a password manager software that creates a unique password for each account?
Gosney: Having a password manager create a unique, machine-generated password for every sign-in service is by far the best way to do it.
But ultimately, we have to get rid of passwords, and I say that as a password cracker! From a security perspective, passwords are pretty terrible. We’re trying to pin the security of an account on the user’s ability to come up with a secret that’s supposed to secure everything. That’s a large responsibility for users. Ultimately, that burden has to shift away from the user to the backend.
Instead of passwords, we should use something like FIDO, which allows users to log in using a security key or biometric information. The biometric approach has some drawbacks for accessing services anonymously, but for the average user, this makes their world more secure without placing the burden on them to have all of their security hinge on their ability to come up with some uncrackable word.
As always, thanks for reading.
Best,
Julia Angwin
The Markup
(Additional Hello World research by Eve Zelickson.)